
Google researchers have uncovered the first concrete evidence of threat actors utilizing artificial intelligence to craft zero-day exploits, autonomous Android backdoors, and sophisticated automated supply chain attacks targeting platforms like GitHub and PyPI.
The Dawn of AI-Powered Cyberattacks
While AI models have previously been employed by hackers for tasks such as generating convincing phishing pages and identifying basic security vulnerabilities, a new report from Google Threat Intelligence Group (GTIG) reveals a significant escalation. Attackers are now harnessing AI to develop advanced zero-day exploits, marking a critical turning point in the landscape of cyber warfare.
Unmasking AI's Fingerprints in Malware
GTIG researchers identified a compelling attack scenario where threat actors bypassed two-factor authentication (2FA) using a Python script on a web-based administration tool. To their surprise, this proved to be a zero-day exploit. Although initial suspicions pointed to Claude Mythos, this was later deemed unlikely.
“For the first time, GTIG has identified a threat actor using a zero-day exploit that we believe was developed with AI.”
Further analysis of the code uncovered distinct characteristics pointing to machine authorship. Unlike human-written code, these scripts featured “an abundance of educational docstrings” and even a fabricated, “hallucinated but non-existent CVSS score,” strong indicators of AI generation.
The blog post from Google noted that groups primarily from the People’s Republic of China (PRC) and the Democratic People’s Republic of Korea (DPRK) are at the forefront of these AI-driven tests. Entities like APT45 and UNC2814 are leveraging AI to meticulously scan for flaws, often training their AI models on vast datasets like ‘wooyun-legacy’ – a collection of 85,000 historical security cases – to emulate expert auditors.
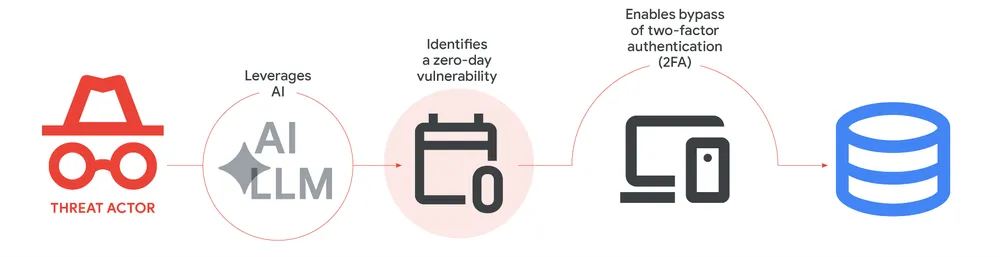
Attack Chain (Source: Google)
The Rise of Autonomous Agents and Advanced Reconnaissance
Hackers are also deploying Large Language Models (LLMs) for sophisticated target scouting, significantly enhancing the effectiveness of phishing lures. They prompt these models to map out intricate company hierarchies or pinpoint specific hardware utilized by a target. This advanced ‘environmental fingerprinting’ allows attackers to tailor their assaults with unprecedented precision.
Researchers also observed a growing preference for ‘agentic workflows,’ where tools such as Hexstrike and Strix are employed to execute complex multi-stage tasks. For instance, a PRC-nexus actor was found using these tools in conjunction with the Graphiti memory system to conduct an attack on a Japanese technology firm.
Escalating Supply Chain Threats and Deepfake Campaigns
In early February 2026, the PROMPTSPY Android backdoor emerged, utilizing a ‘GeminiAutomationAgent’ to monitor phone screens and simulate button clicks. By late March 2026, a group identified as TeamPCP (also known as UNC6780) launched a significant attack on the software supply chain. They injected malicious code into popular tools like LiteLLM and Checkmarx. Leveraging the SANDCLOCK credential stealer, they successfully exfiltrated AWS keys and GitHub tokens, likely for extortion purposes.
Finally, Google researchers highlighted the increasing use of AI in information operations. A pro-Russia campaign dubbed Operation Overload employed AI voice cloning to impersonate journalists in fabricated videos, spreading disinformation. While these sophisticated tactics continue to evolve, Google is actively combating these threats using its own AI-powered defensive tools, such as Big Sleep and CodeMender, to automatically detect and remediate vulnerabilities.
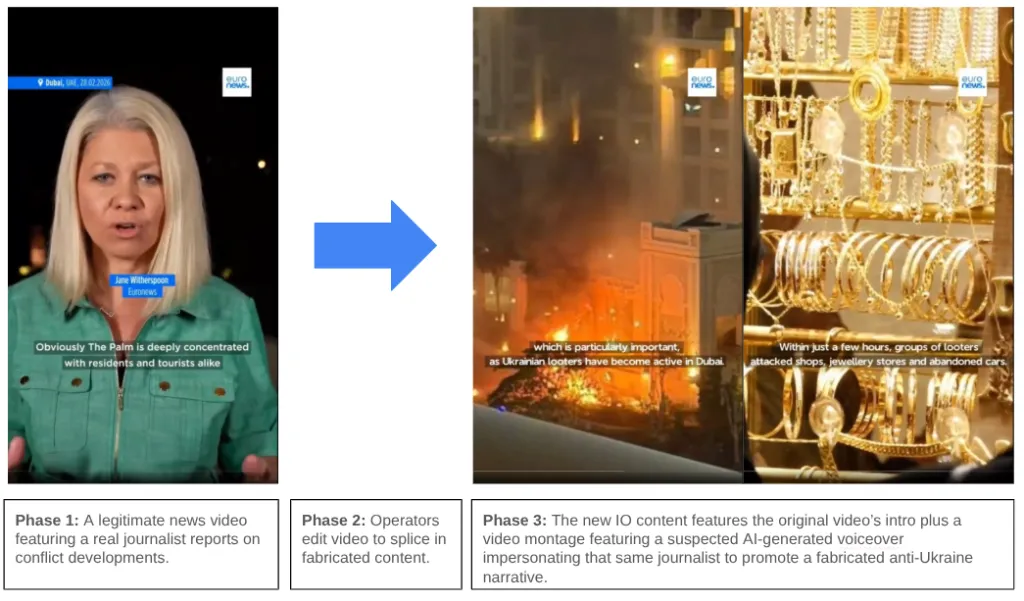
(Source: Google)
